A few years ago, I discovered TryHackMe, and it completely changed how I approached learning cybersecurity. The platform breaks down complex topics in a way that’s easy to understand and combines that with hands-on labs that simulate real-world scenarios. It doesn’t just focus on “hacking” either—there’s training for blue team strategies, reverse engineering, web application security, cryptography, OSINT, penetration testing, IoT security, malware analysis, and more. It’s one of the best tools I’ve come across for building practical skills in this field.
What really hooked me was how TryHackMe gamifies learning. I remember dedicating over three months of daily training to earn the coveted 90-day streak flame. That gamification was what kept me coming back every day—it made learning challenging topics feel fun and rewarding.
This December, I decided to jump back in and participate in their annual Advent of Cyber event. It’s a 24-day challenge where participants solve a new cybersecurity task each day, often inspired by real-world scenarios. This year, they added a bonus “hard mode” called the Side Quest, which involved finding four hidden keycards scattered throughout the main event. Naturally, I couldn’t resist giving it a try.
Finding the L1 Keycard
The first keycard, L1, was hidden in the challenges from Days 1 to 4. Here’s how I tracked it down:
Day 1’s Clues: The task centered around a malicious YouTube-to-MP3 converter site created by an attacker named “Mayor Malware.” The main event provided a starting point: a GitHub user linked to the attack. However, no other details were given. Using OSINT techniques, I explored the first GitHub user’s activity and noticed they had interacted with a second user. Digging into this second user’s repositories, I found one that contained source code for a Command-and-Control (C2) server.
Investigating the Code: The second user’s repository included default admin credentials and a Flask secret key used for signing session cookies. By comparing this repository with Mayor Malware’s forked version, I discovered an oversight: while the admin credentials had been updated, the original secret key had been left unchanged.
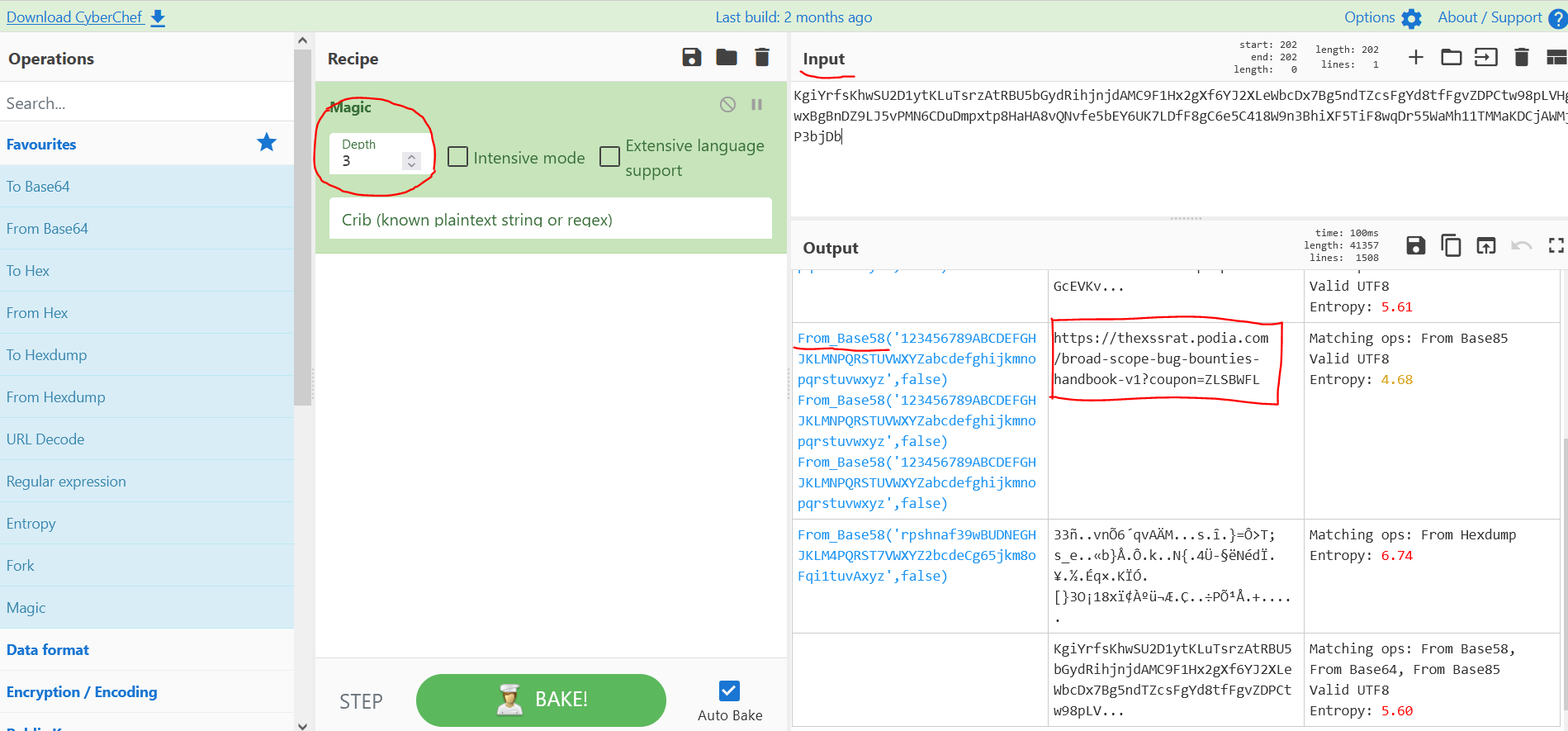
Exploiting the Oversight: Using the Flask secret key and a Python tool called
flask-unsign, I generated an admin session cookie. After injecting the cookie into the browser, I gained admin access to the C2 server.Finding the Keycard: With admin access, I navigated the server’s dashboard and data pages, uncovering sensitive stolen user data. Among this data was the L1 keycard and its password:
vK5RMlvkGO3QlLU.Unlocking the Side Quest ZIP File: Using the keycard’s password, I extracted the Side Quest ZIP file, which contained a packet capture (PCAP) file for the first Side Quest task.
The entire process was a reminder of how important it is to methodically investigate every angle. It was a great mix of OSINT, web application security, and even some cryptographic concepts like cookie forgery.
Progress and Reflections
After analyzing the packet capture from the ZIP file, I’ve managed to uncover two of the four answers needed to complete the first task. The remaining two answers are still a work in progress, but just finding the L1 keycard was a rush. It’s moments like these that remind me why I’m so passionate about cybersecurity. The thrill of the hunt and the satisfaction of piecing together clues make all the effort worthwhile.
Since completing the Advent of Cyber, I’ve been diving into other training on TryHackMe, including several one-off capture-the-flag challenges. A few years ago, my 90-day streak put me in the top 6% of TryHackMe users. Over time, I had fallen out of the top 10% and hovered somewhere around the 15-20% range (TryHackMe only shows exact rankings for users in the top 10%). Recently, though, I’ve climbed back into the top 6%, and I’m proud of that progress.
Cybersecurity is a constant challenge, and the field often feels like an uphill battle, but platforms like TryHackMe make the learning process rewarding. Whether you’re just starting out or looking to hone advanced skills, I can’t recommend it enough.